CATEGORY
Physical Security Services in India
Vendor Rationalization is performed by carrying out a spend analysis, by which low/major spend suppliers are identified along with their service capabilities. It is then followed by eliminating the incumbent low spend suppliers and selecting primary suppliers to engage with based on geographic/service capabilities and requirements.
Beroe LiVE.Ai™
AI-powered self-service platform for all your sourcing decision needs across 1,200+ categories like Physical Security Services in India.
Market Data, Sourcing & Supplier Intelligence, and Price & Cost Benchmarking.
Schedule a DemoThe World’s first Digital Market Analyst
Abi, the AI-powered digital assistant brings together data, insights, and intelligence for faster answers to sourcing questions
Abi is now supercharged with GPT4 AI engine. Enjoy the ease of ChatGPT, now on Abi
Physical Security Services in India Suppliers
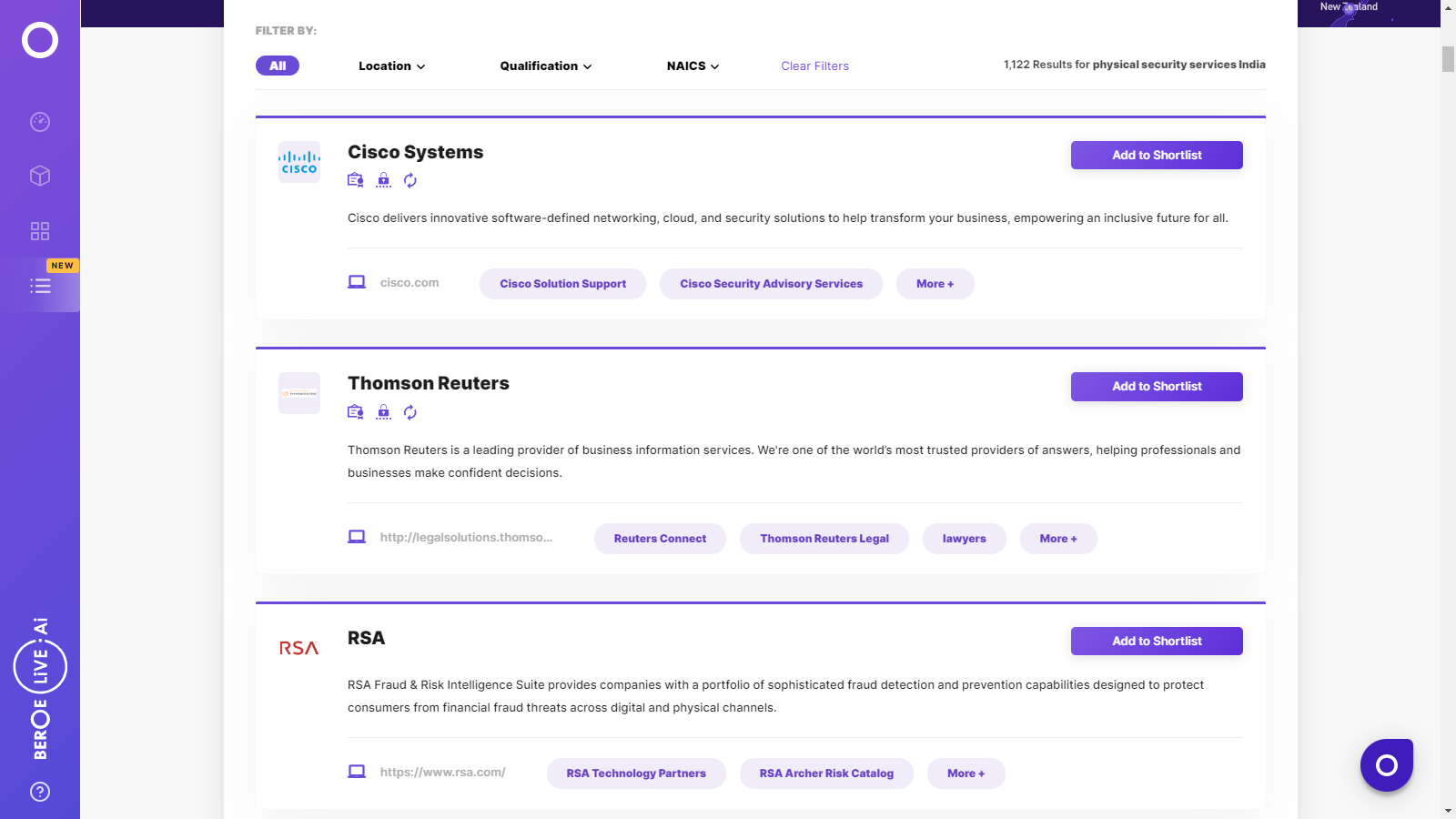
Find the right-fit physical security services in india supplier for your specific business needs and filter by location, industry, category, revenue, certifications, and more on Beroe LiVE.Ai™.
Schedule a Demo


Use the Physical Security Services in India market, supplier and price information for category strategy creation and Quaterly Business Reviews (QRBs)
Schedule a DemoPhysical Security Services in India market report transcript
Regional Market Outlook on Physical Security Services in India
- Vendor consolidation through spend analysis is the most experimented way of cost reduction
- In case the company has already consolidated the supplier base, security service providers shall help the company in rationalizing the number of security guards deployed by replacing a part of security guards with electronic security systems (security integration)
Key Industry Trends
Security as a Service:
Physical security services are moving toward a system that provides more specific solutions, as well as a higher level of integration and service. Instead of viewing physical security as a series of connected hardware and software systems, the industry has started to move toward system that provides more of security as a service to successfully run security operations.
Deeper Convergence of Physical and Logical Security:
The upcoming convergence of physical and logical security is an absolute certainty, which is already in progress. For example, Role-Based Access Control (RBAC) has been the predominant model for access control in the IT world of logical security and today, this architecture is reflected in the design of leading access control systems, because it significantly reduces the cost of access management.
Shift from Proprietary to Open Hardware:
Security dealers and integrators have started to manufacture hardware that are compatible with third-party operable software. This is mainly because of the issues customers faced in the past, due to the manufacturer's negligence in updating the software or discontinued operations. The customers feel guaranteed with the invention of these open hardware, which can also be run on other third-party operating software (apart from OEM).
More Focus on Video Analytics:
The security industry has started to develop video analytics software that works in a similar way to software that analyzes numerical and text data. Instead of having a person to work through video footage, the software can work in real time to help make quick and informed decisions. This would help professionals address several challenges, such as facial recognition, forensic analysis, and perimeter protection.
Integrated Cloud Systems:
Integration of various security systems in an organization has been the trend for quite some time and now the cloud storage is being utilized to achieve maximum operational efficiency through integration. This not only integrates the security systems in an organization, but also provides the user a remote access to the security network, which could be used in techniques, such as intrusion prevention, which is different from intrusion detection.
Drivers and Constraints
- The technology is a two-edged sword, on one hand adoption of new technologies (such as CCTV and electronic surveillance system) reduces cost and on the other, there is a threat for data security, which increases the demand
- Technological advancement has been driving the industry and has developed an urge for progress of cyber security tools to protect cloud storage and data privacy
Drivers
- The increasing demand for security services in different segments and the arrival of new entrants had lead to more competition among service providers and higher fragmentation in the US and Europe
- Increasing threat of cyber security and terrorism has influenced organizations to advance the safety values, thus promoting industry growth
- Factors, such as growing expenditure on the security of critical infrastructures, rising adoption of cloud-based data storages, and data analytics employed by the organizations are fueling the market
Constraints
- Lack of awareness about new technologies and security devices among buyers might result in slower adoption of electronic security services, especially in emerging regions
- The availability of skilled labor force in emerging regions is quite lower compared to mature markets, like Europe and the US. This results in increased training cost and reduced quality of services
- Absence of correlation among security solutions and privacy concerns against the installation of surveillance cameras are hindering the market growth
Interesting Reads:
Discover the world of market intelligence and how it can elevate your business strategies.
Learn more about how market intelligence can enable informed decision-making, help identify growth opportunities, manage risks, and shape your business's strategic direction.
Get Ahead with AI-Enabled Market Insights Schedule a Demo Now
